Folding Phones, and the Road to Get There
Brick Phones The first portable phones were barely portable at all. A suitcase with a [...]
The iPhone’s Hard Reset Bug
Apple Apple’s proprietary software is notoriously difficult to make malware for. It’s not that it’s [...]
The EA Hack
The EA hack isn’t a special case. Not anymore. Hack, after hack, after hack, data [...]
Why So Much Criticism?
The Internet The internet, once a source of incredible interconnectivity, has slowly turned into a [...]
What’s a Wizard?
You’ve seen it before. Sometimes it’s during updates, sometimes one comes with a game, but [...]
How to make Form Fillouts Frustrating
1) Don’t Allow “Overflow” Ever try to type in your phone number, but the field [...]
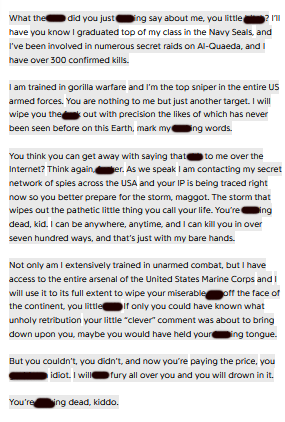
Internet Phenomena: the CopyPasta
What makes a good CopyPasta? Copypasta is a term invented for the internet phenomenon of [...]
Nov
Facebook is Horrible for Information
The 2016 and 2020 elections were some of the tensest elections Americans had ever faced, [...]
What is -Core? Why is it All Online?
Subcultures: The Big Ones Alternative, Goth, Emo, and Punk may be indistinguishable to someone outside [...]
Stop Asking For Free Labor In Your Ads
It’s one thing when a corporation’s business account asks for interaction. It’s another when they’re [...]