Game Data is Getting Ridiculous
Why are game downloads so ridiculously huge? The first Doom game is famous for how [...]
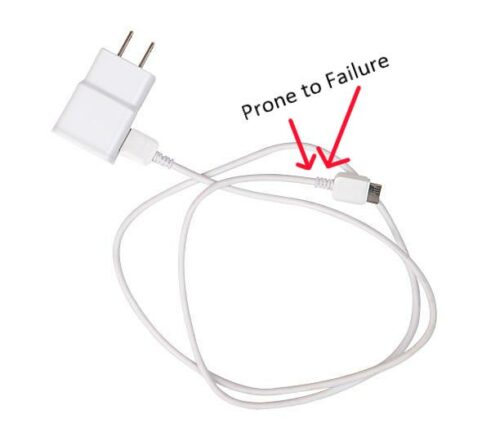
Why Can’t You Tape a Cord Back Together?
Have you ever wondered why just taping a cut cord back together doesn’t fix it? [...]
Sep
Car Screens – Is It a Good Idea, Really?
We all know how addictive screens are. And yet, after endless campaigns to get teenagers [...]
Stop Hyping Autopilot
It’s not done yet!! Tesla’s autopilot is really impressive. It’s just not done yet. Between [...]
Internet Of Things: Network Vulnerability
Internet of Things items are convenient, otherwise they wouldn’t be selling. At least not [...]
Domain Squatting
You’re trying to get to a popular website run by a large soda company. [...]
A History of UFO-Spotting
Eyewitness Accounts and The News – 1940’s on I’ll start when the modern day [...]
Nintendo, and Always Underproducing
Is it intentional? It’s difficult to say. Artificial Scarcity, the process of deliberately limiting [...]
Selfie Culture
Pictures, for the sake of Memories There’s nothing wrong with snapping pics at a concert, [...]
Selfie Related Injuries and Deaths – Why?
Dangerous Dangerous selfies are becoming a distinct sort of rash. Situations that wouldn’t normally be [...]