Don’t Plug In Found USB Sticks
Did you find a seemingly normal USB stick on the ground outside your work? How about in the lobby, where the public can come and go as they please? Did you find something that doesn’t seem to be your company’s preferred brand of USB stick, or even not branded at all? Is it strangely heavy for a typical USB stick?
DON’T plug it in. Here are some reasons why.
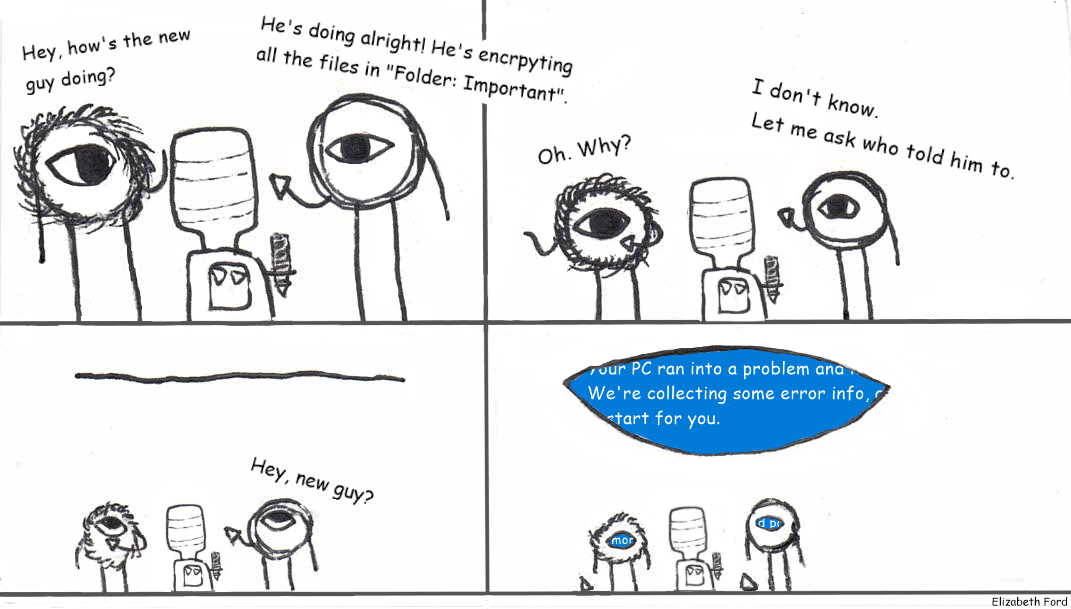
Ransomware
As it’s now 2020 and WannaCry has made the news more than once, you’ve probably heard of ransomware, a type of malware that encrypts files, and threatens to destroy them if money is not sent to the hacker.
USB sticks are one of many ways this virus finds itself into your most important files, pictures, and documents, and it’s notoriously difficult to get rid of. In the time it takes to discover it and attempt to neutralize it, the hacker can simply *poof* the files away if they realize you’re not going to pay.
And deleting them isn’t the only way they can cause pain. Copying the files somewhere and then releasing them online can be disastrous for certain industries and businesses, even worse than just destroying the files, and the hackers know that.
Do NOT plug strange USB sticks into your device. Even if it looks like someone from your office might have dropped it, if you don’t recognize it? Don’t plug it in. Keep it on your desk or turn it in to the IT department and wait for them to come looking for it.
Broad Malware
If the ultimate goal of the USB isn’t money, malware is another widely used way to completely wreck a computer. Sometimes malware is aiming to destroy a business’s computer network, or looking to steal secrets without ransom, or infect other computers on the network and eventually break them all at once. This is where something like AI-driven antivirus comes in handy: if something is propagating very quickly across all the devices on a network, and it’s not officially licensed, and it’s bringing a bunch of .exe stuff with it – antiviruses designed around behavior and not fingerprinting will take notice. They aren’t impenetrable, but it takes more to get around them than it does to get around a classic antivirus.
Again, don’t fall victim to Social Engineering and plug in a USB you found on the floor.
USB Killers
If you thought your anti-virus was enough to stop something nasty from creeping in on a USB, you’d be wrong. There’s more than one way to go about breaking a machine.
A USB killer is a device meant to cause harm to the device’s hardware. Essentially, it takes charge from the computer with a capacitor and then redirects it back. “How much damage could the power flowing to the USB port actually cause?”, you may ask. USB killers aren’t simply redirecting the energy back into the computer at a one-unit-in one-unit-out basis. Instead, they use a capacitor. A capacitor behaves kind of like a balloon rubbed on a carpet: it stores charge in a ‘field’ (the balloon in that example) passively. It doesn’t really matter how much power is leaving the USB port, as long as there is power – when the capacitor gets to its limit, it discharges back into the computer, like the static shock you’d get from the doorknob after scooting across the carpet in socks, but many times larger. Up to 215 volts larger, according to Hackaday.
USB killers are becoming rarer, but they aren’t extinct.
But Why?
So why would someone want to use a USB killer or destructive malware, instead of using ransomware or straight file-stealing?
There are a lot of answers.
Some people just want to break expensive things, and don’t care what that is. Some people are looking to slow down business opponents or gauge weaknesses within the organization. Sometimes something expensive or hard to replace is stored on the computer, and the hacker wants it gone. Sometimes it can even boil down into terrorism, depending on the industry.
The long and the short of it is that you shouldn’t plug in a USB if you don’t definitely recognize it as yours.
Sources: https://resources.infosecinstitute.com/topic/usb-killer-how-to-protect-your-devices/