Category Archives: IT Support
Why Is The Monitor Flickering?
You may notice when filming certain lights on your phone, they seem to flicker, even [...]
Options Beyond the 4:3 Monitor
Most screens use a ratio that optimizes for reading side-to-side, meaning they’re wider than they [...]
Moderator Bots: Baby Steps
In a world of ever-growing conversations and large forums, moderating manpower is in high [...]
What Drives Ants Towards Electricity?
Ants. If you were on the internet just a few years back, you might have [...]
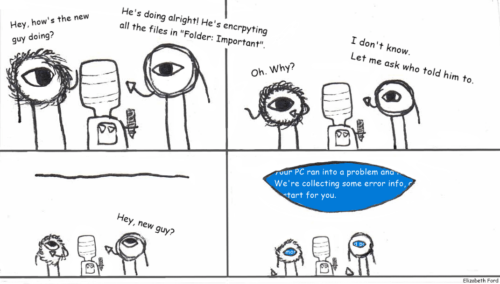
Don’t Plug In Found USB Sticks
Don’t Plug In Found USB Sticks Did you find a seemingly normal USB stick on [...]
Dec
How to Destroy a Hard Drive (Accidentally): A List of Common Items and “Hacks”
1. Those fancy Neodymium (or rare-earth) magnets. Strong magnets can erase credit cards and fuzz [...]
Cybersecurity – Firewalls
As we explained previously, cybersecurity is the defence of computers and devices from damage or [...]
CyberSecurity – Secure configuration
As we found out in the last article, cybersecurity is an important part of every [...]
Cybersecurity – An introduction
Cybersecurity is the practice of defending internet-connected systems such as; computers, electronic systems, networks, and [...]
What’s a cookie?
What’s a cookie? A browser cookie is a little snippet of data that the browser [...]
Oct
- 1
- 2